Products
ASPIS, A Hardware Based Secure Drive
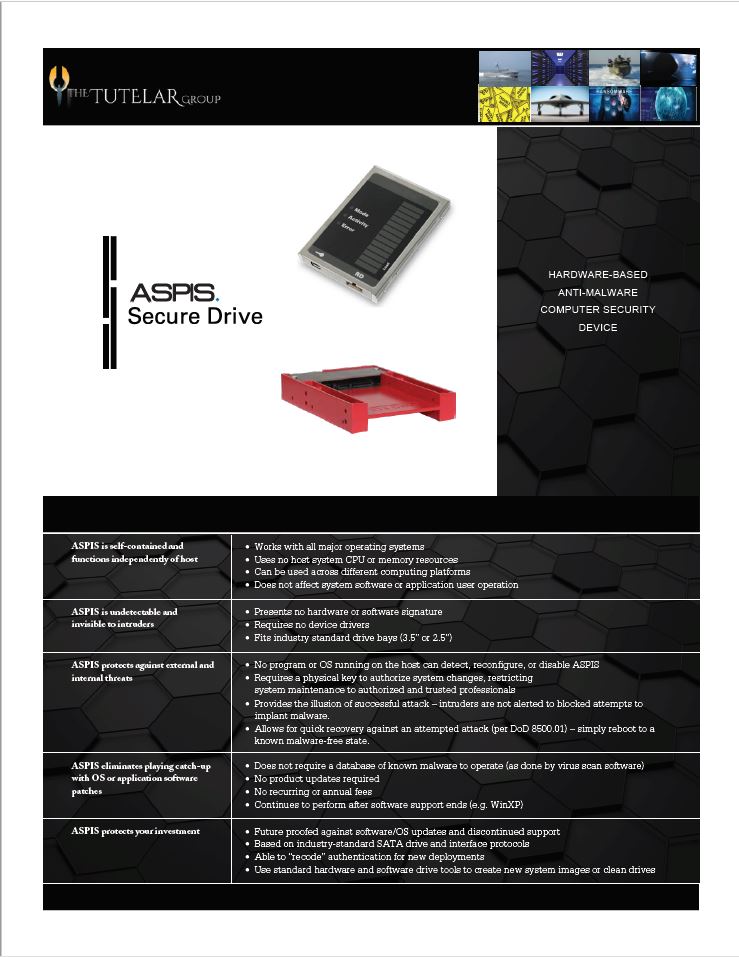
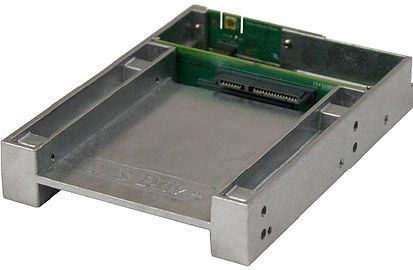
The Advanced System Protection Integrated Shield (ASPIS®) Secure Drive is a game-changing hardware solution to address the never- ending battle to maintain the highest levels of organizational cyber security. The ASPIS Secure Drive prevents unauthorized changes to a computer’s system environment and in doing so, prevents malware from taking hold and becoming persistent. ASPIS can also restore a system to its last known good configuration in a matter of seconds, with a simple reboot. In a marketplace filled with myriad software solutions, firewalls, and other applications, ASPIS hardware elegantly simplifies and enhances computer security.
THE NEW ASPIS APPROACH
Malware can effectively compromise a computer system because of its ability to make unauthorized changes to that system. Unauthorized system changes can be nefarious, well-meaning, or just accidental. No matter how a change occurs, it can become a mess for the IT professional to clean up. A cleanup can take days, weeks, or sometimes months. Even a quick recovery is rarely all that quick. And after the effort is completed, there remain nagging thoughts about whether all of the unauthorized changes were found and addressed.
It is time to consider a new approach, one that is hardware- based and cannot be disabled or altered by any software running on the system. One that addresses the core
of the problem and protects the system whether the operating system is running, the latest software patches are installed, or the IT administrator forgot to follow a step in some process. This new approach is the ASPIS Secure Drive.

HOW MALWARE WANTS TO CHANGE YOUR COMPUTING SYSTEM
For malware to thrive, it needs access to a computer system and rights to the targeted data–either for exfiltration or to control the data in some other way (e.g. ransomware). Remove either of these attributes and the malware is rendered impotent.
ACCESS:
To gain access to a system, malware attacks follow a few basic approaches. This is true whether an attack is launched externally or internally. While details of attacks change and mutate over time, the basics remain the same.
For example, a very common approach is called phishing– the use of online communications to trick someone within an organization to launch the malware or launch code that opens a back door that then allows malware to be downloaded in small portions and build into an attack over time.
An attack might also be initiated by an insider launching similar code, either knowingly or unknowingly, via thumb drive (for example). The insider could be an employee using the computer network or a contractor who is servicing a system within the facility–even a system not directly related to the computer network itself. This code also opens a back door that allows the attack to be downloaded and built over time.
In either case, to initiate the damaging malware, i.e., downloading the payload, requires a change to be made to the system–a change that needs to survive a reboot the of the host system. Stop this access and the attack will not proceed.

PRIVILEGES:
Along with access, malware normally needs to escalate its rights or privileges before completing its task. Malware often positions itself to work around current operating system or third-party software defenses at the next boot cycle.
No matter the method of access, or the method of privilege escalation, the component most targeted by malware, in any system, is the system drive. Protect the system drive and you have drastically reduced your attack profile and increased the stability and uptime of your network.
The Tutelar Group brings this critical anti-malware solution to the market. Our custom software and Subject Matter Experts can help you tailor a custom solution for your company. Please contact us for more information.